Hypothesis
Own intelActive Threat Hunting 24/7
Ciberia's hunting starts with proprietary intelligence, sector activity, and weak signals from your environment to look for what has not surfaced through automatic detection yet.
01 / 04
We hunt the threats your automated defences do not see: APTs, lateral movement, and hidden access before impact.
More than 500 MITRE TTPs covered. No infrastructure changes.
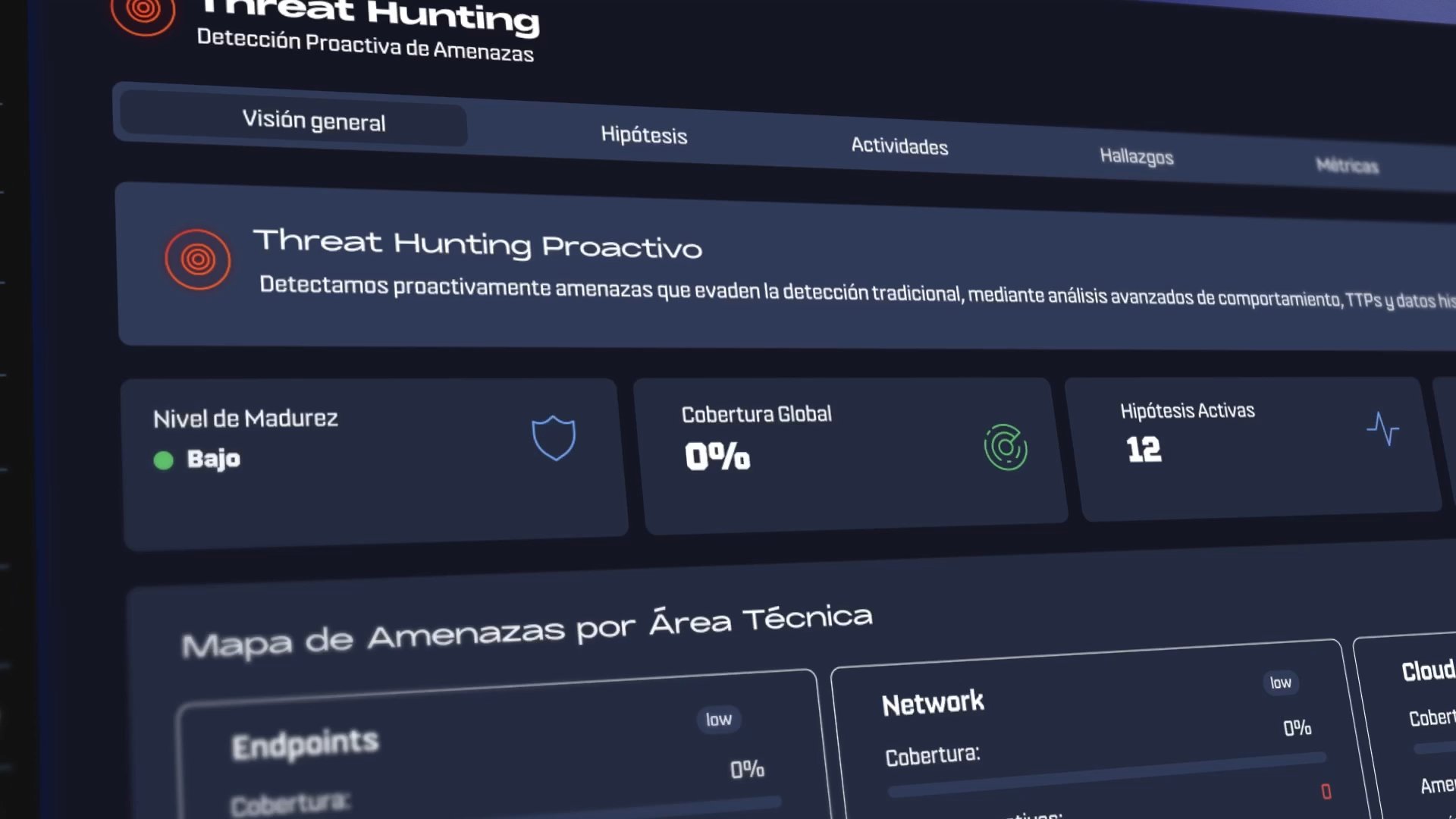
Hypothesis
Own intelCiberia's hunting starts with proprietary intelligence, sector activity, and weak signals from your environment to look for what has not surfaced through automatic detection yet.
01 / 04
Ciberia Platform
Every finding, hypothesis, and detected TTP is documented and accessible from the Ciberia platform.
Integrations
We connect to any technology: SIEM, EDR, cloud, and firewalls.
Status
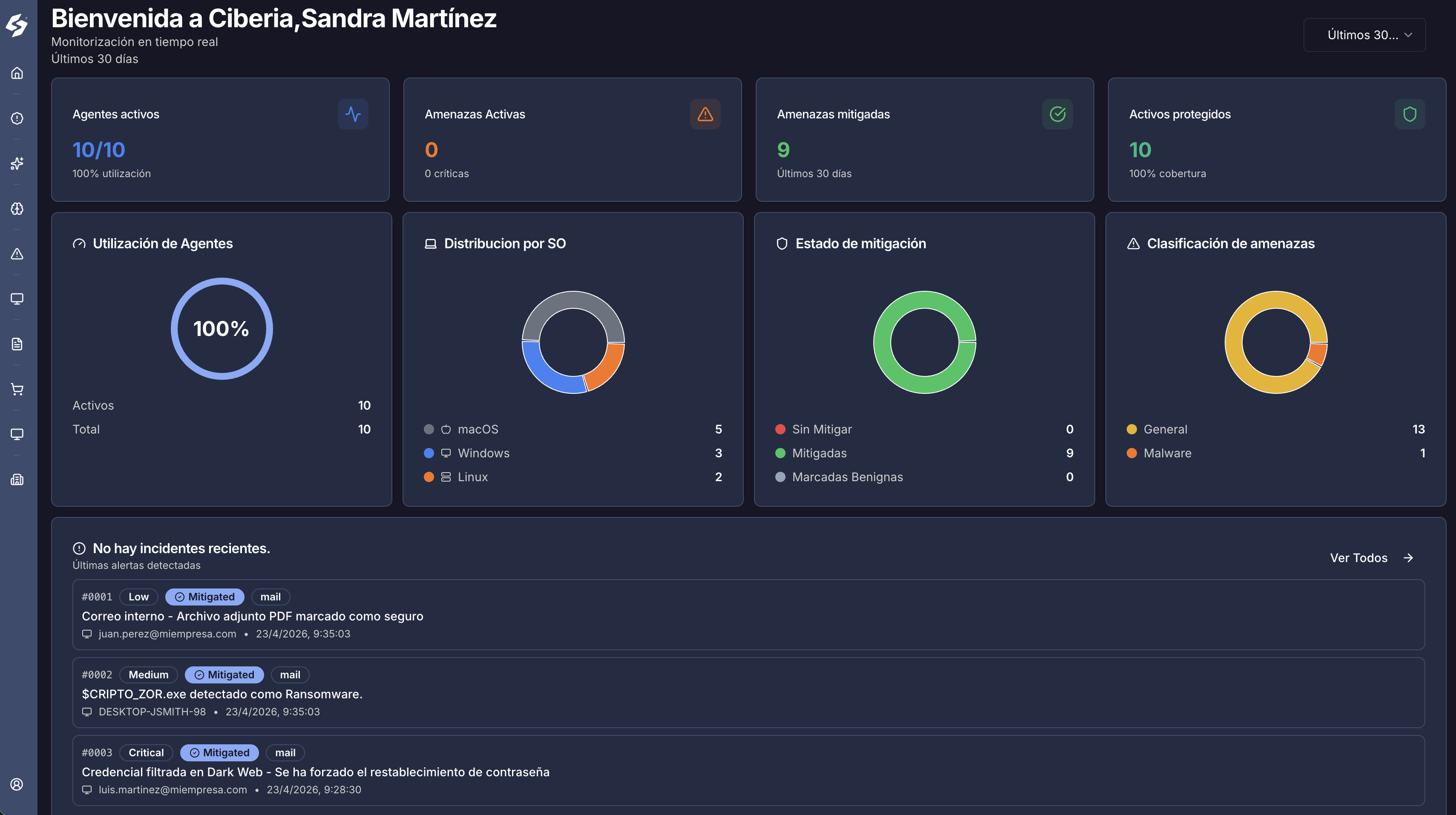
Visualise your organisation's cybersecurity posture in real time.
Alerts
All recent alerts and detected threats in one centralised dashboard.
Integrations
We connect to any technology: SIEM, EDR, cloud, and firewalls.
Status
Visualise your organisation's cybersecurity posture in real time.
Alerts
All recent alerts and detected threats in one centralised dashboard.
Capabilities
We analyse infrastructure looking for indicators, MITRE techniques, and anomalous behaviours.
We detect advanced persistent threats that may have spent weeks inside the network.
Each hunt uses Ciberia IOCs, TTPs, and sector context.
Findings with evidence, potential impact, and prioritised recommendations.
The problem
APT groups move slowly and use legitimate tools to stay below automatic rules.
FAQ
Hover over each question
Discover how our cybersecurity solutions can transform your company's protection.